In the rapidly evolving landscape of information technology, ensuring secure communications has become paramount. As threats become increasingly sophisticated, traditional methods are often rendered obsolete. DK7 emerges as a groundbreaking solution, promising a new era of robust and resilient communication infrastructures. This innovative framework leverages cutting-edge cryptographic algorithms and decentralized architecture to prevent security breaches and safeguard sensitive data.
- Boasting its advanced encryption protocols, DK7 ensures that communication remains confidential and untraceable, shielding users from malicious actors.
- Furthermore, the decentralized nature of DK7 eliminates single points of failure, making it highly resilient to attacks and disruptions.
- As a result, DK7 empowers individuals and organizations to conduct secure transactions, share sensitive information with confidence, and protect their digital identities in the ever-present threat landscape.
DK7's advanced security features position it as a leading contender for the future of secure communications. Its potential to revolutionize industries such as finance, healthcare, and government is undeniable. By embracing DK7, we can pave the way for a more secure and trustworthy digital future.
Harnessing the Power of DK7 Encryption
DK7 encryption stands as a robust encryption standard. Its sophisticated design offers impenetrable protection for your valuable data. By utilizing advanced cryptographic techniques, DK7 reliably thwarts even the advanced cyberattacks.
- Organizations seeking uncompromising data security should without hesitation consider implementing DK7 encryption.
- Its versatility makes it ideal for a broad range of applications, encompassing online banking.
Additionally, DK7 encryption is constantly developed website to keep pace with the evolving threat landscape
Exploring DK7's Features
DK7 stands as a groundbreaking platform in the field of data analysis . Its robust functionalities enable users to efficiently analyze complex data sets, generating actionable knowledge. DK7's user-friendly interface makes it readily available to beginners , {fostering collaboration and innovation across various domains.
- DK7's key features include:
- Data visualization
- Anomaly detection
Protecting Your Data with DK7: Best Practices and Guidelines
Leveraging the capabilities of robust security protocols is crucial for safeguarding your sensitive data. Implementing best practices and guidelines guarantees the integrity and confidentiality of your information. , To begin with, it's essential to configure strong authentication measures, such as multi-factor login, to prevent unauthorized access.
- Furthermore, keep current your DK7 software and hardware to patch any weaknesses that could be exploited by malicious actors.
- Leverage data protection, both in transit and at rest, to protect your information, making it unreadable to unauthorized individuals.
- Consider a comprehensive data backup strategy to retrieve your information in case of cyberattacks.
Continuously monitor your DK7 system for any suspicious activities or abnormalities. By adhering to these best practices and guidelines, you can effectively mitigate risks and safeguard your valuable data with DK7.
DK7 vs. Other Cryptographic Solutions: A Comparative Analysis
When analyzing the strength of cryptographic methods, DK7 often presents itself as a viable contender. Comparing it with other established protocols reveals both similarities and unique properties. DK7's structure often emphasizes speed, while other solutions may strive for privacy in a alternative manner.
- Moreover, DK7's implementation can sometimes be simpler compared to sophisticated alternatives.
- However, one should note that the most appropriate solution depends the specific needs of each application.
As a result, a comprehensive evaluation that considers various factors is essential for making an informed decision regarding the most suitable cryptographic solution.
The Impact of DK7 on Cybersecurity Landscape Influence of DK7 on the Cybersecurity Domain
DK7, a revolutionary exploit framework, has profoundly altered the cybersecurity landscape. Its features allow attackers to rapidly exploit various systems and applications. This poses a substantial threat to organizations worldwide, requiring a comprehensive response from the cybersecurity community.
Consequently, organizations are increasingly implementing new security measures to mitigate the risks associated with DK7. Security professionals are constantly researching ways to counteract its impact. The future of cybersecurity depends on the ability to competently address the challenges posed by tools like DK7.
 Jake Lloyd Then & Now!
Jake Lloyd Then & Now! Andrea Barber Then & Now!
Andrea Barber Then & Now! Katie Holmes Then & Now!
Katie Holmes Then & Now!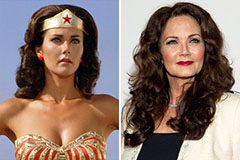 Lynda Carter Then & Now!
Lynda Carter Then & Now! Mary Beth McDonough Then & Now!
Mary Beth McDonough Then & Now!